
The Evolving Cyber Threat Landscape of Modern MFPs
MFPs are at the heart of enterprise cybersecurity risk, and the industry is finally catching up
Check out Keypoint Intelligence’s Cybersecurity page!
MFPs have quietly evolved from simple output devices into sophisticated network endpoints. They process, store, and transmit sensitive business data every day, yet they remain one of the most overlooked attack surfaces in enterprise IT security. Keypoint Intelligence’s 2025 Market Insights study on OEM cybersecurity reveals an industry working hard to close that gap.
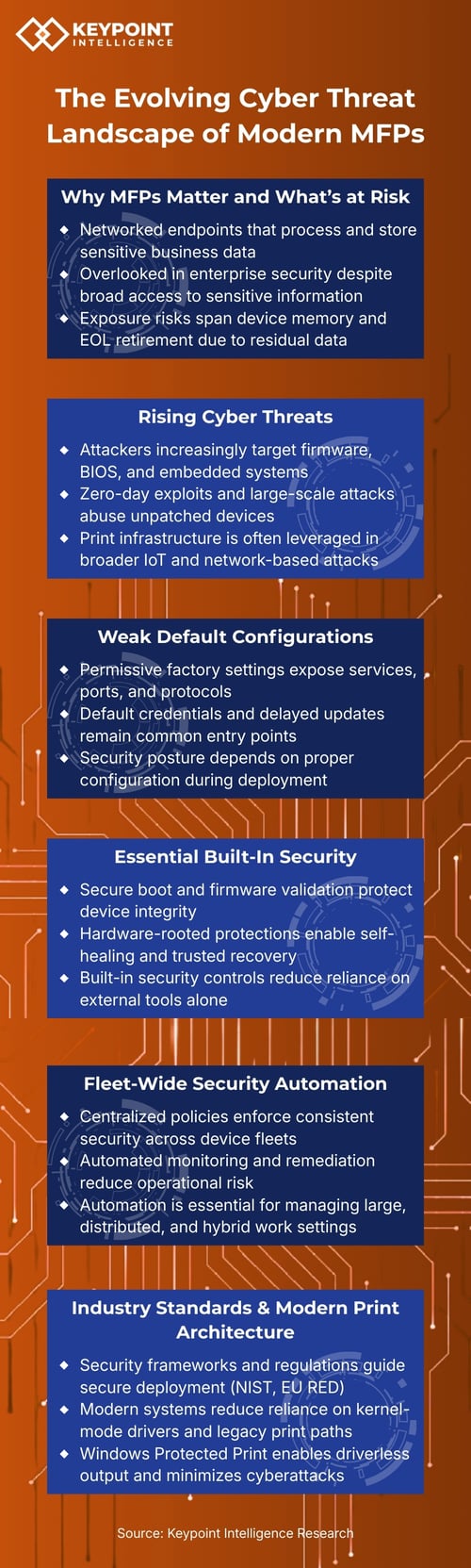
Why MFPs Matter and What’s at Risk
MFPs handle PII, PHI, and confidential business documents, but they rarely receive the same security scrutiny as servers or workstations. Microsoft estimates nearly 10% of network cyber incidents trace back to print infrastructure. Exposure risks span the entire device lifecycle: data at rest, documents in transit, and residual data left on storage media at the end of a lease.
Rising Cyber Threats
Attackers are increasingly targeting firmware, BIOS, and embedded systems, exploiting unpatched devices through zero-day vulnerabilities and large-scale botnet attacks. Print infrastructure is no longer a side door into the network; it is an actively targeted entry point. Post-quantum threats add a further layer of urgency, putting today’s cryptographic foundations at long-term risk.
Weak Default Configurations
Most MFPs ship with all ports and protocols wide open, default credentials intact, and firmware updates delayed. Each of these is a known, exploitable entry point. Security posture should not depend on perfect reseller configuration at deployment—OEMs must take ownership and ship devices “business secure,” and do so by default.
Essential Built-In Security
The strongest security starts at the hardware level. Secure boot, firmware validation, and hardware-rooted runtime intrusion detection ensure that only authorized code runs, and that devices can self-heal if compromise is detected. Built-in controls of this strength reduce reliance on external tools alone and establish a true root of trust.

Fleet-Wide Security Automation
Manually managing hundreds of devices is a compliance gap waiting to happen. Leading OEMs now offer fleet platforms that enforce centralized policies, monitor security deviations, auto-remediate non-compliant devices, and flag outdated firmware with known CVEs. For distributed and hybrid environments, this level of automation is no longer optional.
It’s the foundation of a defensible security posture.
Industry Standards and Modern Print Architecture
NIST CSF 2.0, Common Criteria’s HCD-cPP, and the EU RED Delegated Act (fully applicable from August 2025) now set enforceable security benchmarks for print devices. Meanwhile, Microsoft Windows Protected Print (WPP) eliminates kernel-mode drivers entirely, dramatically shrinking the attack surface that has made client print drivers a persistent vulnerability for decades.
Keypoint Intelligence Opinion
The OEMs in this study have raised the bar significantly. When properly configured, today’s business- and enterprise-class MFPs deliver strong, layered protection. But gaps remain, particularly around default configurations and fleet automation, and closing them requires vendors to go further. The vendors that make this shift from device seller to trusted security partner will be best placed to meet the demands of the modern enterprise.
Stay ahead in the ever-evolving print industry by browsing our Report Store for the latest insights. Log in to the InfoCenter to view related research through our Workplace CompleteView Advisory Service. Not a subscriber? Contact us for more information.

